Opening Pandora’s box - Supply Chain Insider Threats in Open Source projects
TL;DR: Granting repository "Write" access in an Open Source project is a high-stakes decision. We...

TL;DR BoostSecurity.io is thrilled to announce ‘poutine’ – an Open Source security scanner CLI you can use to detect misconfigurations and vulnerabilities in Build Pipelines. Additionally, it can create an inventory of build-time dependencies so you can track known vulnerabilities (CVEs) as well. Today, the tool has about a dozen rules covering vulnerabilities found in GitHub Actions workflows and Gitlab pipelines. We have plans to add support for CircleCI, Azure Pipelines and more. The source code is published under the Apache 2.0 license and it is available on GitHub.
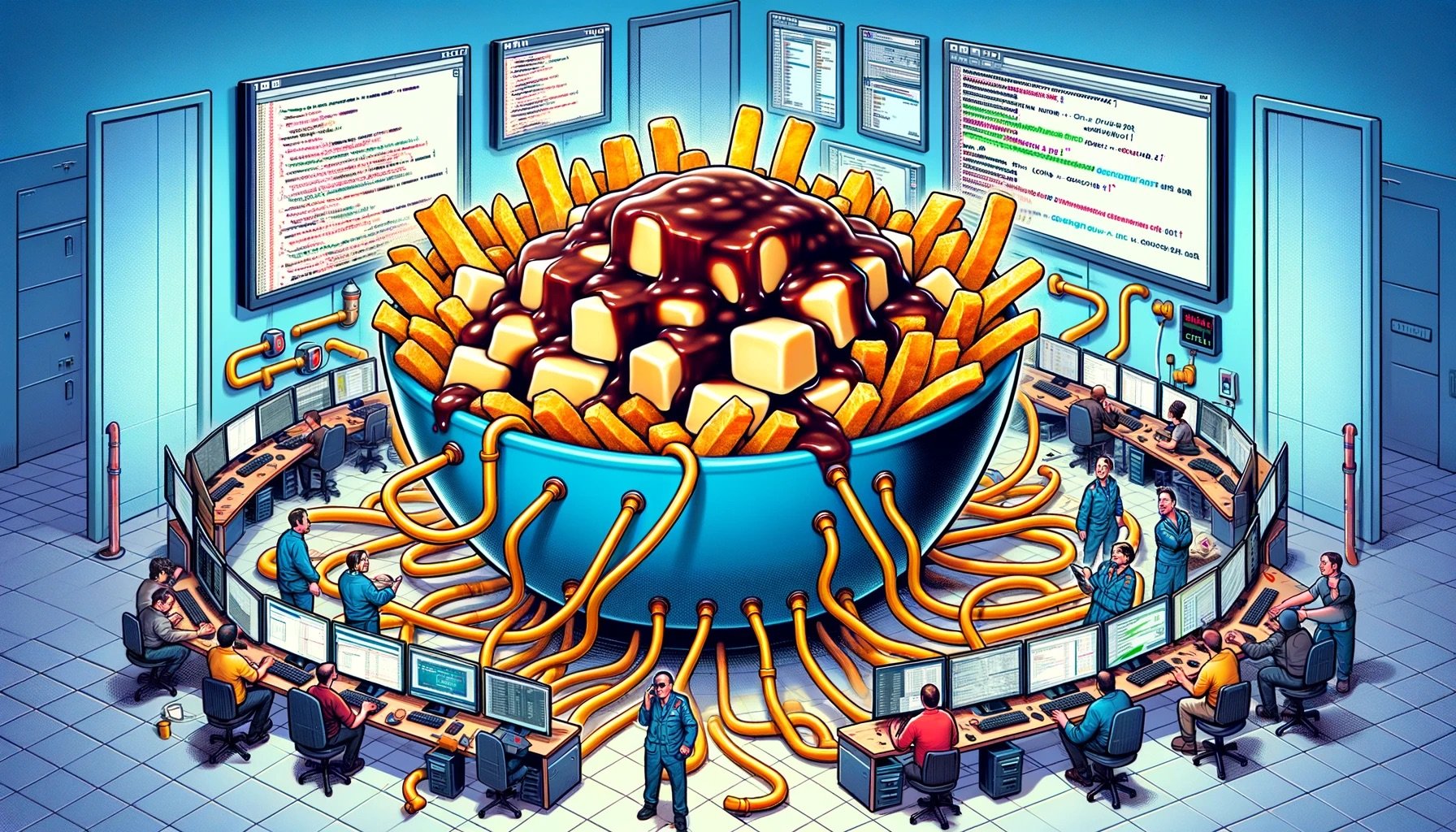
In French, the word "poutine", when not referring to the dish, can mean "messy". Inspired by the sheer complexity and intertwined dependencies of modern Open Source projects, ‘poutine’ reflects both a nod to BoostSecurity’s Montreal roots and the often messy, complex nature of Build Pipelines in the context of securing the software Supply Chain.
You first need to install the CLI locally or configure it as part of your CI/CD itself. Then, you will need an authentication token, which we recommend you scope down using fine-grained personal access tokens (PATs) to the minimum set of permissions required (i.e. read-only access to repository contents) and visibility (i.e. Public and/or Private repositories). You can target a single Git repository (remote or local) or an entire GitHub (or Gitlab) organization and the tool will fetch the list of repositories and scan them in parallel.
The tool was designed to perform a shallow and sparse Git checkout of only the relevant files (namely YAML) which means it is amazingly efficient, even on large Git repositories, and thus can typically churn through organizations containing hundreds of large repositories in a handful of minutes.
As of the Public Beta (v0.9.*) release, the tool supports 10 major categories of issues, in turn, each rule detects several variants of different scenarios. You can find the detailed, up-to-date, documentation here. Just to highlight the two most serious ones: it detects Injections with Arbitrary External Contributor Input and Arbitrary Code Execution from Untrusted Code Changes. The latter essentially detects risky usage of so-called Living Off The Pipeline tools, another Open Source project from our team which we’ve discussed in the past.
A unique feature is the ability to create an inventory of the Build-time dependencies, such as GitHub Actions, Gitlab pipeline imports, Docker containers, CircleCI orbs, etc. Effectively creating an SBOM of build dependencies, which is simply ignored by all the most common SBOM tools out there. At the moment, the list of known vulnerable components (CVEs) of this category is suspiciously small. Our intuition is that this is really just the tip of the iceberg. We’ve been researching this area for a while now and we know for a fact that there are numerous 0-days out there in this space - we’ve responsibly disclosed some ourselves.
When we started our research in this area, we’ve created a very detailed attack tree for GitHub Actions. We’ve used it as a guiding principle when designing the tool so that we initially focus on real-world attack scenarios which we know can be exploited by external attackers, with little to moderate skill and leaving very little indicators of compromise (IoCs) in some cases.
Given that we wanted a way for us, and for you, to test the capabilities of the tool, we’ve created the MessyPoutine project. It is a classic “goat project” for GitHub Actions designed as a Capture The Flag contest where you can exploit workflows in about a dozen different ways. The challenges range from trivial to very challenging.
We hope that people can learn how easy to exploit some of those real-world attack scenarios and it attracts more eyeballs to this space.
To install ‘poutine’, download the latest release from the releases page and add the binary to your $PATH.
$ brew install boostsecurityio/tap/poutine
$ docker run ghcr.io/boostsecurityio/poutine:latest
$ poutine analyze_local .
$ poutine -token "$GH_TOKEN" analyze_repo messypoutine/gravy-overflow
$ poutine -token "$GH_TOKEN" analyze_org messypoutine
$ poutine -token "$GL_TOKEN" -scm gitlab -scm-base-uri https://example.com org/repo
The source code is published under Apache 2.0 on GitHub and we would love to get your feedback, ideas, bug reports as well help us with the features listed in our public roadmap. We have ambitious goals with this project to make it become the preferred scanner in this niche of Supply Chain. We’re only scratching the surface with the current feature set and we already find it tremendously useful in our research.


TL;DR: Granting repository "Write" access in an Open Source project is a high-stakes decision. We...

TL;DR: Our deep dive into open source projects’ CI/CD systems has revealed that build pipelines...